What is YOUR Organization doing to survive the Commercial & Public Security Transformation?
-
Strategic
Imperatives -
Growth
Gap -
The Yellow Brick
Road -
Transformational
Growth
Strategic Imperatives For Commercial & Public Security
Ensuring responsible collection, usage, and storage of data to safeguard individual privacy, mitigating the risk of fines, and maintaining customer trust.
Embracing digital transformation for security and shifting from analog to connected solutions, leaving obsolescence behind, and ensuring future-ready protection.
Integrating cybersecurity policies into operational processes to protect against digital threats and ensure comprehensive security in the era of digital transformation.
How do you shift from where you are to what you want to become? How do you fill the gap?
Based on those strategic imperatives the gap between where you are now and where you need to be to achieve transformational growth is daunting.

Effective Growth Coaching increases productivity by over 53%

Over 40% of professionals would like to have more meaningful networks

84% of Executives say Innovation is critical but lack resources
The Three Components Required for Transformational Growth
Growth Opportunities for Commercial & Public Security

Digital Intelligence
- Digital Intelligence Platforms
- Open-Source Intelligence (OSINT) Platforms
- Social Media Intelligence (SOCMINT) Platforms

OT Cybersecurity
- Critical Infrastructure Cybersecurity
- Government Cybersecurity
- IoT/IIoT Cybersecurity

Identity Security
- Biometric Software Solutions
- Digital ID
- Fraud Detection & Prevention
- Identity & Access Management
Digitized Physical Security
- Access Control Solutions
- Screening & Detection Systems
- Digital Surveillance Solutions
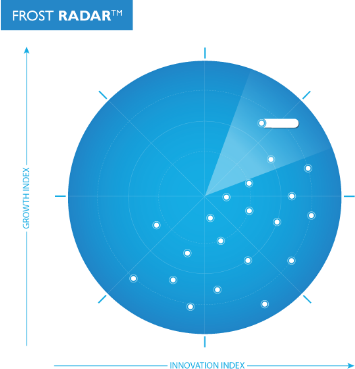
Frost RadarTM
Benchmarking Your Future Growth Potential
Our work is focused exclusively on identifying the growth opportunities of the future and evaluating companies that are best positioned to take advantage of them. The Frost Radar™ is a robust analytical tool that allows us to evaluate companies across two key indices: their focus on continuous innovation and their ability to translate their innovations into consistent growth.
To discover how you benchmark
against competition
A PRACTICAL, HIGH IMPACT, SCALABLE TRACKING SOLUTION
Measure with The Growth
& Innovation Index
-
2
Major Indices
-
10
Analytical Algorithms
-
1
Platform
Recognizing Excellence and Leadership in Security for 20 years
Our best practices analysis provides in-depth examination of successful strategies and tactics used by leading companies across all industries, and offers recommendations for implementation to drive performance and success
Experience
Analysts
Connect with the Brightest Minds in Growth Innovation Leadership
Our community activates your success with our peer-to-peer network, peer meetings, annual growth events, executive roundtables, and access to inspiring activities such as our innovation workshops.
Join our exclusive community of like-minded professionals today.
Join Growth CommunityGrowth Webinars

How can biometric systems minimize user friction and maximize office security?

Will innovative fraud prevention systems eliminate digital identity threats?

Will evaluating security in connected mobility networks drive customer value?

Enriching public safety with the magic of advanced first-responder technologies

Mastering OT security: mitigation and resilience strategies

Which C-suite strategies will fortify your converged security environment?

Why upgrading government cybersecurity policies is critical in the connected era

Unmanned systems & security: a critical transformation in operational efficiency

Can the proliferation of IoT security strategies rejuvenate healthcare security?

Innovations in airport security: transforming best practices for a safer future

Will new-age threat analytics empower your business to contextualize risks?

How can intuitive perimeter detection solutions help advance border security?
Activate your transformational journey
Through growth coaching you will gain the tools necessary to develop powerful growth pipeline strategies that will fuel the future of your company.
Growth Coaches | Think Tanks | Growth Experts
Growth for Leaders & Companies
Maximized through collaboration
Continuous flow of Growth Opportunities
Proven Best Practices
Optimised Customer Experience
Implementation Excellence
Industry Leadership
"*" indicates required fields